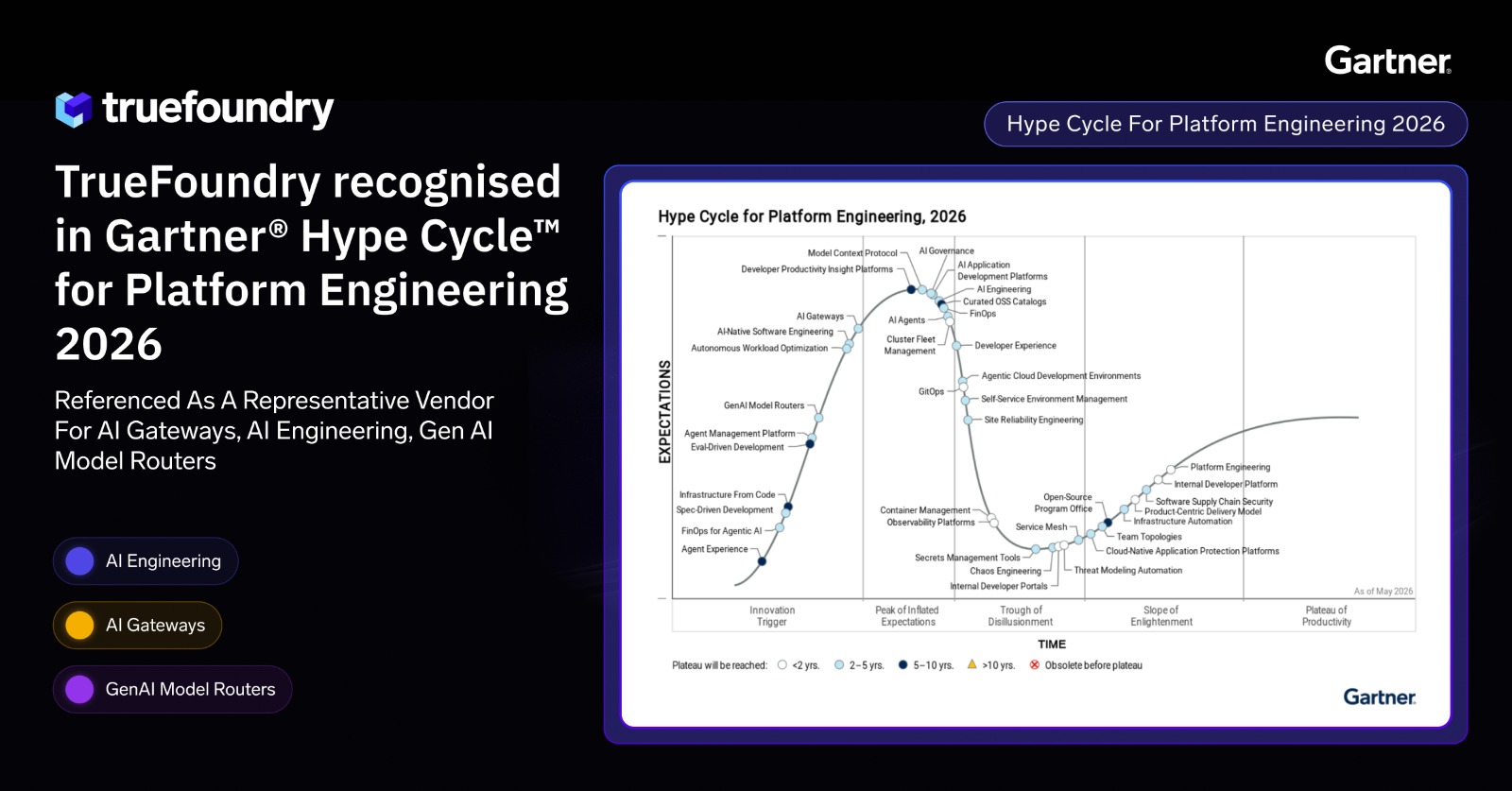
MCP Gateway Registry: The Enterprise Control Plane for AI Agents
.webp)
Diseñado para la velocidad: ~ 10 ms de latencia, incluso bajo carga
¡Una forma increíblemente rápida de crear, rastrear e implementar sus modelos!
- Gestiona más de 350 RPS en solo 1 vCPU, sin necesidad de ajustes
- Listo para la producción con soporte empresarial completo
You have moved beyond chatbots. Now, your teams are building autonomous AI agents that access your internal databases, query Jira, update GitHub, send Slack messages, and call your custom APIs, all without human help. These incredible agent workflows unlock real productivity gains, but they also introduce governance complexity that most teams underestimate.
At first, this setup works. What starts as an interesting experiment , where a developer connects one agent to one tool, which runs smoothly. Soon, more agents and MCP tools are added, whether sourced from VS Code extensions, community servers, or internal builds. Before long, IT loses track of how many connections exist, where credentials are stored, or which agent can access what.
This is not just a technical headache. It is also a security and compliance risk waiting to happen.
Anthropic launched the Model Context Protocol (MCP) in November 2024 to standardize how AI agents connect with external tools. MCP fixes the integration language issue, but it does not address governance. It does not help you manage hundreds of tool connections across many agents at enterprise scale.
That is where an MCP gateway registry helps. Let us look at what this registry is, what it must do to work in production, where competitors miss the mark, and why TrueFoundry is a better, more cost-effective choice.
.webp)
The Chaos Before the Registry: Point-to-Point Tool Integrations
When enterprises start building AI agents without a central registry, they almost always follow the same path. The first few integrations are simple. After that, things start to break down in predictable ways.
- Hardcoded Dependencies: Developers connect their agents directly to specific MCP servers. Each agent knows where the tool is, how to call it, and which credentials to use. This setup works for a single source. But if the backend tool's API changes, every agent relying on it breaks at once. There is no buffer to handle the change, so platform teams have to update multiple codebases to fix the same issue.
- Credential Sprawl: Every agent manages its own authentication. API keys get hardcoded into environment files. OAuth flows get stored in individual servers and developer notebooks. Service account credentials end up duplicated across teams. When a key needs to be rotated, it has to be tracked down and updated in every place it lives. If one instance gets missed, that is your exposure window. At scale, secure credential rotation becomes nearly impossible to guarantee.
- Zero Central Visibility: IT and security teams do not have a single point of access to check. They cannot easily answer questions like which MCP tools and data sources agents can use, which agents are using which tools, how often a database is queried, or if an agent is accessing data it should not. Compliance audits mean gathering logs from many systems, and spotting anomalies is nearly impossible.
These are not edge cases, and they are a leading cause of shadow ai exposure. They show up in every enterprise that tries to scale agent infrastructure without a control plane. The point-to-point model works for early adopters experimenting with individual agents. It does not work for production.
What Is an MCP Gateway Registry?
An MCP gateway registry is a central catalog inside your MCP gateway. This acts as the single source of truth for every approved tool in your organization. It is the one place where every approved MCP server and external tool is registered, described, versioned, and made discoverable to AI agents across your organization.
Think of it as the directory for your AI tool infrastructure. Just as microservice catalogs abstract away individual service endpoints, a registry abstracts away raw protocol support complexity from agent developers. Like a service catalog shows development teams which APIs exist in a microservices setup, an MCP gateway registry tells AI agents which MCP tools they can use, how to call them, and what permissions they have.
- Centralized Publishing: A platform engineer registers a tool once in the official MCP registry. After that, any authorized agent in the organization can find and use it, including common utilities like search, document retrieval, and internal API access, without the engineer needing to send connection details to each team. The registry is now the deployment target for tools, not individual tools managed by each agent.
- On-the-Fly Discovery: Agents do not use hardcoded tool settings. Instead, they query the registry at runtime to get the latest schemas, descriptions, and instructions for the tools they are allowed to use. This dynamic tool discovery means when a backend API changes, the registry updates and agents pick up the change automatically. You no longer have to update prompts every time a tool changes.
- Single Source of Truth: Your security teams get a unified inventory. Every AI-accessible tool in the organization is registered in one place, with ownership, access control policies, and usage history attached. Everything is visible. Nothing operates out of sight. This becomes the true system of record for all agent-accessible tooling.
.webp)
Core Capabilities of an Enterprise Registry
Not every tool registry is built for enterprise use. A basic catalog that lists tools and endpoints is a starting point, not a solution. In production, there are four capabilities that separate the best MCP gateway registry from a well-organized configuration file.
Granular Role-Based Access Control (RBAC)
In any real organization, different AI agents serve different functions and should operate with different levels of access control. A customer support agent needs to look up order records and escalate tickets. It should not have visibility into database administration commands. A finance agent needs access to payment systems. It should not be able to trigger deployment pipelines.
An enterprise registry enforces this at the visibility level, not just the execution level. AI agents do not see MCP tools they are not authorized to use. The access control policy and control logic are applied before discovery, not after a call attempt fails. This means policy enforcement is not a guardrail bolted on after the fact. It is built into the architecture of how tools get surfaced.
RBAC in a proper registry is tied to identity. It integrates with your existing enterprise identity providers, whether that is Okta, Azure AD, or a custom SSO setup, so that the permissions AI agents inherit are governed by the same policies that govern human access across your organization.
Seamless Tool Versioning
Backend APIs change. That is not a risk to be avoided; it is a reality to be managed. An enterprise registry handles this by letting platform teams publish multiple versions of a tool simultaneously.
Version one stays in the registry and continues to serve agents that depend on it. Version two gets registered alongside it. Development teams can point specific agents at version two for testing. Once the team is confident the update is stable, production agents migrate on their own schedule. There is no forced cutover, no downtime, and no broken agents because a tool changed underneath them without warning.
This parallel versioning model is how mature infrastructure teams manage any shared dependency. The favorite part for platform engineers is that they no longer need to coordinate forced upgrade windows. The registry brings that same discipline to AI agents and their MCP tools.
Centralized Authentication Vaulting
In a direct-connect model, every agent is responsible for its own credential storage. That means API keys, OAuth tokens, and database connection strings scattered across agent codebases alongside other software artifacts in environment variables and configuration files across your infrastructure. Rotating a single key requires finding every place it lives. Missing one creates a vulnerability window.
A registry with centralized credential vaulting removes this problem. Backend credentials are stored in a single place and managed by the gateway. When an agent calls a tool, the gateway injects the appropriate credential at runtime. The agent never sees the raw key. Developers never need to manage downstream authentication for the tools they call. Token refresh happens automatically. Rotation happens once, in the vault, and every agent immediately benefits.
Individual users authenticate with the MCP gateway once, using a single token. The gateway handles all downstream MCP authentication on their behalf, including injecting custom headers required by specific backend tools.
Full Audit Trail and Observability
In traditional infrastructure, you can pull logs from a server to understand what happened during an incident. With distributed agent-tool interactions, that becomes much harder when there is no central collection point.
An enterprise registry gives you that collection point. Comprehensive audit logging records every tool call with the agent identity, the user or service making the request, the arguments passed, the response returned, and the latency of the interaction. When something goes wrong, you can trace exactly what the agent did, in what order, and what each tool returned. Compliance teams get an auditable record without having to build custom instrumentation for every tool individually
.webp)
The Hidden Flaws in Competitor Registries
Several options exist for managing MCP servers at scale. Most of them solve part of the problem. Understanding where they fall short helps clarify what you actually need when evaluating the right registry for your organization.
- Configuration File Nightmares: Community registries such as the JFrog MCP registry and other open source MCP proxy tools manage tool registration through static YAML or JSON configuration files, including approaches built around Docker Compose and Nginx reverse proxy setups. Every new MCP server requires a manual file edit, a commit, and a redeployment. At small scale this is workable. As the number of MCP tools grows and teams multiply, it becomes a bottleneck. There is no UI for non-engineers to register tools, no approval workflow, and no way to see at a glance what the current state of the registry actually is. The configuration file becomes the single source, and it is always one missed update behind reality.
- The Enterprise Paywall: Several AI infrastructure SaaS platforms offer basic MCP gateway routing for free, then gate the features that actually matter behind enterprise contracts. RBAC, SSO integration, tool versioning, and comprehensive audit logging are not advanced features. They are the baseline requirements for any production deployment. When those capabilities are locked behind an unpredictable pricing tier, your governance posture depends on a budget conversation, not a technical decision.
- Data Egress and Sovereignty Risks: Cloud-hosted SaaS registries process your agents' dynamic tool discovery requests through infrastructure you do not control. In regulated industries, this creates immediate security risks. Every discovery request potentially carries metadata about your internal systems, the tools your AI agents use, and the sensitive data they are accessing. This is a supply chain concern as much as it is a data risk. Routing that through a third-party cloud, even one you trust, may put you on the wrong side of your own data residency requirements before a single tool is ever called. Treating MCP servers as software supply chain components means applying the same scrutiny as any third-party code dependency. This is a key operational risk that security teams consistently flag.
.webp)
How TrueFoundry Simplifies Tool Management
TrueFoundry designed its registry to solve the real challenges enterprises face when moving AI agents from experiments to production. The most significant unlock is that governance does not require a separate tooling layer; it runs inside your own infrastructure. The architecture focuses on three priorities: data sovereignty, operational simplicity, and governance that does not slow down developers.
Absolute Data Sovereignty (In-VPC Deployment)
TrueFoundry runs the entire registry and MCP gateway inside your own cloud account, whether it is AWS, GCP, or Azure. Tool traffic, agent telemetry, credentials, and dynamic tool discovery requests stay within your network. They never pass through TrueFoundry's infrastructure or touch the public internet.
For organizations with SOC 2, HIPAA, or internal data residency needs, this is not just a checkbox. It is the difference between a platform that fits your mcp security model and one that needs a long exception process before use. When everything runs in your VPC, your security teams only need to review your own infrastructure. The single control plane remains fully within your security perimeter.
Transparent, Compute-Based Economics
TrueFoundry does not use feature gating to charge enterprises more. Granular RBAC, credential storage, full dynamic tool discovery, and comprehensive audit logging are standard features, not add-ons for higher pricing tiers.
Costs are based on your actual compute usage. As you scale your agent infrastructure, you pay for the compute you use, not for access to governance features that should be standard. This means the features you need to run safely in production are available MCP servers governance from day one, no matter your contract tier.
Built for Developer Velocity
Publishing, testing, and versioning tools does not require editing YAML files or submitting configuration changes through a deployment pipeline. Developers interact with the official MCP registry through an intuitive UI or CLI. Platform teams can register new MCP server entries, set access control policies, and push updates without creating manual work for every consuming team.
TrueFoundry organizes MCP servers into logical groups using MCP Server Groups, which allows teams to isolate toolsets by environment, function, or security tier. Development teams can experiment with tools without opening up access in the production registry. Different groups carry their own RBAC policies and approval flows, so high-risk sensitive systems require explicit sign-off before an agent is allowed to call them.
The platform also supports On-Behalf-Of (OBO) MCP authentication. Rather than AI agents operating under a generic service account, the MCP client tool calls can reflect the identity and permissions of the actual human user interacting with the agent. The MCP tools respect the same access boundaries that person has everywhere else in the enterprise systems.
.webp)
Conclusion: Treat Tools as Infrastructure
The pattern is consistent across enterprises that have scaled AI agents past the proof-of-concept stage. Point-to-point connections between agents and tools work until they do not. The moment you have more than a handful of agents operating in production, the absence of a central registry becomes a daily operational problem, not a theoretical risk.
Broader mcp adoption across enterprises makes this infrastructure layer increasingly essential. An MCP gateway registry is not a nice-to-have layer on top of your agent architecture. As organizations move along the adoption curve from single agents to coordinated multi-agent systems, the registry becomes the foundation on which everything else depends.
It is the control plane that governs agent infrastructure. It is how IT teams get visibility, how security teams enforce policy enforcement, and how developers ship tools without creating manual work for every team that wants to access tools.
TrueFoundry keeps all of that inside your own environment. Your company systems stay protected, and your data never leaves your cloud perimeter. The MCP registry runs in your VPC. The credentials stay in your vault. The audit trail belongs to you. And the features you need to run safely in production are available without a pricing conversation.
TrueFoundry AI Gateway ofrece una latencia de entre 3 y 4 ms, gestiona más de 350 RPS en una vCPU, se escala horizontalmente con facilidad y está listo para la producción, mientras que LitellM presenta una latencia alta, tiene dificultades para superar un RPS moderado, carece de escalado integrado y es ideal para cargas de trabajo ligeras o de prototipos.
La forma más rápida de crear, gobernar y escalar su IA




























.webp)














