What Is AI Security? Definition, Threats, and How Enterprises Respond
.webp)
Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
AI systems are no longer isolated experiments running in sandboxed environments. They are now the center of live business operations, connected to internal databases, customer-facing applications, HR systems, financial records, and automated workflows. They receive real data, process it, and act on it, most often without a human reviewing each step.
That shift has fundamentally changed the nature of the security problem. An AI system is not a static web application with a predictable surface. It ingests external content, reasons over it, calls tools, and generates outputs that downstream systems trust and act on. The attack surface looks different. The failure modes look different.
Traditional cybersecurity assumes deterministic behavior. Given the same input, traditional systems produce the same output, and their behavior can be bounded and tested. AI systems do not operate that way. They are probabilistic, context-sensitive, and capable of generating novel outputs based on input data they were never explicitly programmed to handle. That shift alone expands the security problem beyond what static rule-based defenses were designed to manage.
The controls required to govern AI security are different from anything the traditional security stack was built to handle.
This guide explains what is AI security in practice, why the threat environment has changed significantly in 2025 and 2026, the specific security risks enterprises face today, and what effective protection actually looks like when AI moves from experiment to production infrastructure.
.webp)
What Is AI Security?
What is AI security in practical terms? AI security is the discipline of protecting AI systems, including their AI models, training data, inference pipelines, agent workflows, and surrounding infrastructure, from threats that can compromise their integrity, availability, or confidentiality.
The AI security definition covers two interconnected concerns that most organizations need to address simultaneously.
Security for AI focuses on protecting AI systems themselves. This includes defending AI models against adversarial attacks, securing the data sources that feed them, governing access controls, and continuous monitoring of their behavior in production. It treats the AI system as an asset requiring protection in the same way an enterprise protects a database or an API.
AI for security refers to the use of AI capabilities to strengthen how organizations detect threats, respond to incidents, and analyze risk across their broader infrastructure. AI-powered threat detection, automated anomaly detection, and AI-assisted vulnerability discovery all fall under this category.
Most enterprise AI security conversations in 2025 and 2026 center on the first concern, because the second requires the first to be solved. AI security for the broader enterprise cannot be trusted unless security for AI systems is already in place. Otherwise, organizations risk deploying AI tools that extend their attack surface while attempting to defend it.
This establishes a dependency order. AI for security operations cannot be trusted unless security for AI is already in place. Without it, organizations risk deploying AI systems that extend their attack surface while attempting to defend it.
Why AI Security Has Become Crucial in 2026
The urgency is not theoretical. The numbers from the past eighteen months describe an environment where adoption has moved much faster than the governance infrastructure around it.
- The adoption gap is real and widening: Gartner projects that 40% of all enterprise applications will include task-specific AI agents by 2026, up from less than 5% in early 2025. The security frameworks built to govern those agents have not kept pace. Most were designed for static applications, not AI systems that autonomously call tools, read external content, and make decisions that carry data security implications.
- Attacks are accelerating: The IBM 2026 X-Force Threat Intelligence Index recorded a 44% increase in attacks beginning with the exploitation of public-facing applications, largely driven by AI-enabled vulnerability discovery. Ransomware groups increased by 49% year over year. Supply chain and third-party compromises have nearly quadrupled since 2020, a trend that directly threatens AI pipelines and model repositories.
- AI-specific breaches are expensive and hard to detect: According to the 2025 Reco AI Security report, shadow AI breaches cost an average of $670,000 more than standard incidents and take longer to detect, averaging 247 days. 97% of organizations that experienced AI-related incidents lacked basic access controls at the time of the incident.
- Shadow AI is no longer a fringe problem: TThe HiddenLayer 2026 AI Threat Landscape Report found that 76% of organizations now identify shadow AI as a definite or probable problem, up from 61% the prior year. A 2025 LayerX report found that 77% of enterprise employees who use AI tools have pasted company data into a chatbot query, and 22% of those instances included confidential personal information or financial sensitive data.
- Visibility gaps are the norm, not the exception: A 2026 Gravitee survey found that only 24.4% of organizations have full visibility into which AI agents are communicating with each other, and more than half of all deployed agents run without any security oversight or logging. Over 31% of organizations surveyed by HiddenLayer did not know whether they had experienced an AI security breach in the past twelve months.
The gap between deployment pace and AI security readiness defines where the real risk sits right now. Deployment has become continuous, but security posture management remains periodic. AI systems are being shipped, updated, and integrated faster than they can be audited, which creates a persistent window where systems are live, exposed, and not yet governed.
.webp)
What Core AI Security Threats Do Enterprises Face in 2026?
These threats do not exist in isolation. They compound. A prompt injection can exploit over-permissioned credentials. A poisoned dataset can amplify model inversion risk. Shadow AI can bypass every control layer entirely. The challenge is not just identifying individual security vulnerabilities but understanding how they interact across the AI system.
AI systems introduce a new category of threats that sits between traditional cybersecurity and the operational risks of autonomous systems. Understanding what you are defending against is the first step to building a meaningful AI security posture.
Prompt Injection Attacks Turn Trusted Agent Actions into Security Incidents
Prompt injection attacks hold the number one spot on the OWASP Top 10 for LLM Applications in 2025. NIST has tracked a greater than 2,000% increase in AI-specific CVEs since 2022. The reason for this growth is structural, not incidental.
Prompt injection works because there is no hard boundary between instructions and data in a large language model. This is a fundamental design characteristic, not a temporary weakness. As long as models interpret natural language as both data and instruction, the distinction cannot be enforced purely at the model layer. That is why mitigation must happen at the infrastructure and access controls layers.
An attacker embeds malicious instructions inside a document, an email, a web page, or an API response that an AI agent processes as part of its normal workflow. The agent interprets those embedded instructions as legitimate tasks and executes them using its own access and credentials. No exploit code. No network security breach. Just text that the AI system was not built to question.
The consequences scale with agent permissions. Researchers have demonstrated prompt injection in production AI systems including GitHub Copilot Chat, Salesforce Einstein, and ServiceNow's Now Assist, in which a second-order injection caused a higher-privilege agent to export an entire case file to an external URL. When AI agents operate with over-broad permissions, a single successful injection can become a full environment compromise.
Prompt injection is not simply a model flaw that will be patched away. It is an operational AI security risk that requires controls at the infrastructure layer, not just at the model level.
Data Poisoning Corrupts AI Model Behavior Before Deployment Even Begins
Data poisoning attacks target the AI training and fine-tuning pipelines that determine how an AI model behaves before it ever serves a single production request. When training data is corrupted by injecting malicious examples into fine-tuning inputs, attackers can cause an AI model to produce systematically incorrect outputs, or introduce hidden backdoors that activate only under conditions the attacker controls.
In August 2025, researchers at Snyk demonstrated a technique called RAGPoison, which targets retrieval-augmented generation (RAG) systems. The attack injected poisoned embeddings into a vector database, each containing prompt-injection payloads designed to trigger on any related query. The default configuration of Qdrant, a widely used vector database, shipped with no authentication and open CORS settings, making this attack accessible to anyone with write permissions to the database.
Supply chain attacks have become a related and growing vector. The IBM X-Force data shows that large supply chain compromises have nearly quadrupled since 2020. Malware hidden in public model repositories and open-source AI frameworks was the most commonly cited source of AI-related data breaches in the HiddenLayer 2026 report, affecting 35% of surveyed organizations, even as 93% of those same organizations continue to rely on open repositories for their AI development work.
Credential Sprawl Turns Every Compromised API Key Into a Major Exposure
The number of API keys, service accounts, and agent credentials in enterprise environments has grown roughly 100 times in three years. Every new AI agent deployment, every new model integration, every new tool connection introduces credentials that need to be created, stored, rotated, and revoked. In environments without centralized access management, this happens ad hoc.
The result is credentials scattered across cloud environments, developer notebooks, configuration files, and agent codebases across multiple teams. Infostealer malware exposed over 300,000 ChatGPT credentials in 2025 alone. Compromised chatbot credentials do not just give an attacker account access. They can be used to manipulate outputs, exfiltrate sensitive data, or inject prompts into a running AI agent.
Most organizations still assign AI agents to shared service accounts or existing user credentials rather than scoped, purpose-built identities. That architectural decision creates accountability gaps and dramatically expands the blast radius of any single compromised key. When credentials cannot be rotated without hunting down every location they exist, rotation simply does not happen on schedule.
Model Inversion Allows Attackers to Extract Sensitive Training Data Through Queries
Model inversion attacks reconstruct information from an AI model's underlying training data through carefully crafted queries. Attackers exploit the fact that large language models memorize patterns from their training corpora. By querying a production model repeatedly with targeted input data and analyzing its outputs, they can extract fragments of sensitive information that appeared in the training set.
This security risk increases significantly when organizations fine-tune foundation AI models on internal datasets without proper access controls and rate limiting on the inference endpoint. The fine-tuning process teaches the AI model to recognize and reproduce patterns from proprietary AI data. A model fine-tuned on internal contract language, customer records, or source code creates a channel through which that information can potentially be recovered.
The mitigation is not simply to avoid fine-tuning. It is to apply the same access controls, rate limiting, and continuous monitoring to model inference endpoints that you would apply to any database containing sensitive data.
Shadow AI Creates Data Leakage Risk That Security Teams Cannot See or Govern
Shadow AI refers to AI tools, AI models, and AI agents operating inside an organization without security teams knowledge or approval. This is not a fringe behavior. A 2025 CSO Online survey of 2,000 employees found that 49% use AI tools not sanctioned by their employers, and more than half of those employees do not understand how their inputs are stored or analyzed by those tools.
Every unsanctioned AI tool connection is a data protection gap that security teams cannot see, log, or stop in real time. When a developer pastes proprietary code into a public model interface, or a sales team member uploads a client contract to an unvetted generative AI assistant, that sensitive data has left the organization. There is no audit trail, no way to scope the exposure, and no recall process.
Samsung banned ChatGPT after engineers leaked proprietary source code through the platform. That incident surfaced because it escalated. Most shadow AI leakage never surfaces. It accumulates until an audit, a regulator, or an incident forces the question of what security controls actually existed.
.webp)
What Are the Key Requirements for Effective AI Security?
Understanding the threats is the starting point. The controls that follow are not optional enhancements. They are the minimum conditions required to make AI systems governable in production. Without them, the AI system may function, but it cannot be secured. Effective AI security requires technical security controls that work together at the infrastructure layer, not as isolated add-ons applied after the fact.
- Identity-aware execution: Every AI agent action must be tied to a verified human identity with a defined scope of permissions. Shared service accounts make it impossible to answer the basic incident response question of who authorized what. When AI agents inherit the identity of the requesting user through mechanisms like OAuth 2.0 On-Behalf-Of flows, the access they exercise is bounded by that user's existing permissions and every action is attributable.
This is what prevents AI systems from becoming anonymous actors inside your infrastructure. Without identity propagation, every action becomes unattributable, and accountability breaks down at the exact point where automation increases security risks.
- Centralized access control: A governed control plane ensures that access controls are defined once and applied consistently across every model, tool, and AI agent in the organization. Without centralization, access management becomes fragmented across individual deployments, enforced inconsistently, and difficult to audit. Per-team and per-environment RBAC, enforced at the gateway layer before requests reach any model or tool, gives security teams the control they need without creating friction for developers.
- Prompt and output filtering: Automated detection of adversarial inputs and sensitive data in outputs must happen at the infrastructure layer, not inside individual application codebases. Input guardrails that scan prompts for sensitive information, prompt injection patterns, and disallowed content before they reach an AI model, combined with output guardrails that evaluate responses before they are returned to users, create a data governance posture that application-level checks cannot replicate.
- Complete audit trails: Every model call and AI agent action must be logged with full metadata including user identity, agent identity, AI model, tool, timestamp, arguments, and output. Logs must be retained within the organization's own environment to satisfy regulatory requirements under SOC 2, HIPAA, and GDPR. Logs that live in a third-party SaaS system are not fully under your control and cannot be produced on-demand for compliance reviews with the same reliability as logs in your own infrastructure.
- VPC-native deployment: Keeping inference and governance inside the organization's own cloud security boundary eliminates the data security risks that come with routing AI workloads through external SaaS platforms. When every prompt, every response, and every tool call stays within your network boundary, you close the most common path by which proprietary sensitive data leaves your environment without authorization.
.webp)
How TrueFoundry Addresses AI Security at the Infrastructure Layer
TrueFoundry is built around the principle that AI security must be enforced at the infrastructure layer. Security controls that live inside individual applications are inconsistently applied, difficult to audit, and unable to protect against potential threats that arrive at the model or tool layer before application code ever runs.
More importantly, they are bypassable. An attacker interacting directly with a model endpoint or tool layer does not pass through application logic. If the security measures are not enforced at the infrastructure boundary, they are not controls you can rely on.
The platform deploys entirely within the customer's AWS, GCP, or Azure environment. Every inference call, AI agent action, tool execution, and prompt-response pair remains within the organization's cloud security boundary. This architecture eliminates the data security risks that come with SaaS-routed AI platforms, where even well-intentioned data governance depends on trusting that AI data sent to a third party is handled according to your policies.
Innovaccer, a healthcare AI company operating under HIPAA and processing approximately 17 million inference requests per month across clinical workflows, uses TrueFoundry's AI Gateway deployed in AWS GovCloud. Every piece of protected health information touched by their AI systems stays within their own cloud environments. Their audit trails are stored in their own environment and integrate directly into their observability pipeline via Grafana and OpenTelemetry. When a compliance auditor asks for evidence of access controls or data protection, the answer exists in their own logs, not in a third party's dashboard.
Each of the AI security capabilities built natively into the platform maps directly to the threat categories outlined above. This alignment is what turns security from a checklist into a coherent system.
• OAuth 2.0 identity injection: Agents act on behalf of the requesting user, inheriting only that user's permissions. There are no shared service accounts. There are no over-privileged API keys attached to agent identities. Every tool call and model request is attributed to a specific human user, creating an accountability chain that survives compliance review.
• Per-server and per-model RBAC: Access policies are enforced at the gateway layer before requests reach any model or tool. Different teams, agents, and environments see only what their role authorizes. A developer in the staging environment does not inherit access to production models. A customer support agent cannot see tools available to the finance workflow. The policy is defined once, centrally, and applied consistently.
• Prompt filtering and PII redaction: Input guardrails scan every prompt for sensitive data including PII, PHI, prompt injection patterns, and disallowed topics before the request reaches a model. Detected content is either blocked, masked, or transformed depending on the configured policy. Output guardrails evaluate model responses for toxicity, policy violations, and accidental data leakage before responses are returned. The platform integrates natively with OpenAI Moderation, AWS Guardrails, Azure Content Safety, and Azure PII detection, and supports custom rules written in configuration or Python. Each redaction event is logged independently, producing a record of what was detected, what was done with it, and when.
• Immutable audit logs: Every request is logged with full metadata, including user, agent, model, tool, timestamp, and output. Logs are retained within the customer's own environment and can be exported in structured JSON format for offline analysis, compliance reporting, or integration into existing SIEM pipelines. For government workloads, TrueFoundry supports WORM storage via Amazon S3 Object Lock, producing a legally defensible audit trail that cannot be deleted once written.
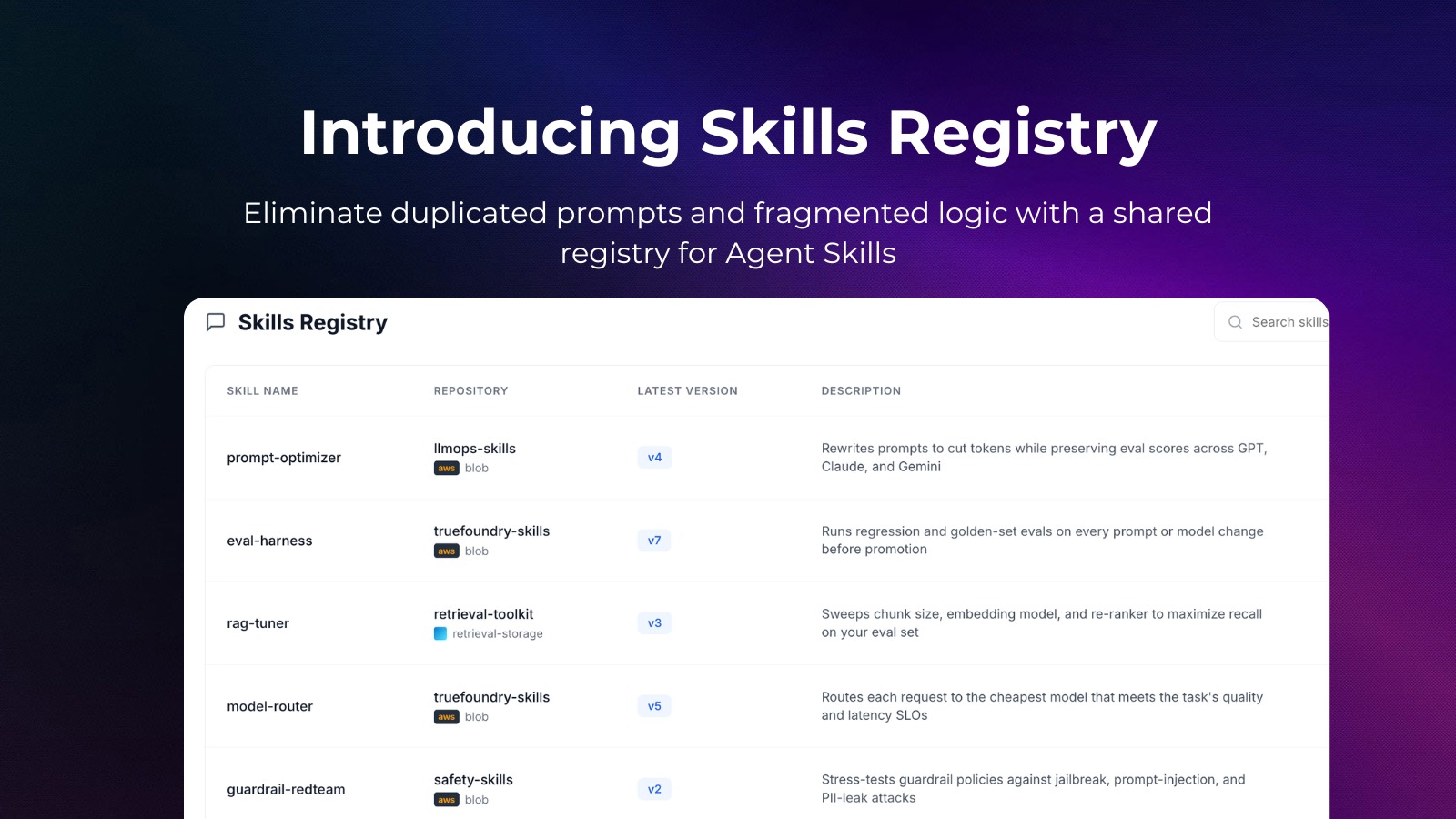
• Virtual MCP Server abstraction: Backend tool implementations can be swapped without exposing new security vulnerabilities to AI agents. When a backend service changes its API or gets replaced, the virtual MCP server layer absorbs that change. AI agents continue to call the same interface. This insulates production AI systems from both infrastructure changes and supply chain risks, where a compromised tool in the registry does not require touching every AI agent that depends on it.
.webp)
Frequently Asked Questions
How can AI be used in security?
AI is used in security to detect threats, analyze risk, and automate response. Machine learning models identify anomalous network behavior and surface indicators of compromise faster than manual analysis. AI-powered tools scan code and infrastructure for vulnerabilities, often finding weaknesses before attackers do.
Security operations teams also use AI to triage alerts, reducing noise and improving response time. As noted in the IBM 2026 X-Force report, attackers are using AI to accelerate vulnerability discovery, which means defenders must use AI to keep pace. The key requirement is that any AI used in security must itself be governed, audited, and protected.
What are the types of AI security?
AI security falls into three main categories.
Model security focuses on protecting the model from adversarial manipulation, data poisoning, and model inversion.
Infrastructure security covers the pipelines, APIs, storage systems, and compute environments that support AI workloads, including access control and network boundaries.
Operational security focuses on how AI behaves in production, including monitoring outputs, auditing actions, and detecting misuse or drift.
Shadow AI cuts across all three, because unsanctioned usage introduces risk at every layer simultaneously.
What are AI security tools?
AI security tools operate at different layers of the stack.
AI gateways, such as those from TrueFoundry, enforce access control, authentication, prompt filtering, and audit logging across all model and agent interactions.
AI security posture management (AI-SPM) tools scan deployments for misconfigurations and over-permissioned identities.
Prompt injection testing tools evaluate systems for vulnerability to malicious inputs.
Vector database security tools protect the RAG layer by controlling write access and validating data sources.
SIEM integrations bring AI system logs into existing security pipelines, giving teams a unified view across both traditional and AI-driven systems.
What is Secure AI?
Secure AI refers to systems built with security embedded throughout their lifecycle, not added after deployment.
A secure system operates with least privilege, uses validated training data, and enforces centralized access control over its inference pipeline. Its inputs and outputs are monitored, and every action is logged. It runs inside the organization’s network boundary, and its identity is tied to a specific user or service, not a shared credential.
Frameworks such as the NIST AI Risk Management Framework and the EU AI Act reflect these expectations.
What is an example of AI security?
Consider a healthcare AI assistant handling patient queries.
Without proper controls, patient data may be sent to external model endpoints, with no audit trail and no guarantee of access isolation.
With AI security in place, the system runs through an in-VPC gateway. Each request is tied to an authenticated clinician. Sensitive data is detected and handled before reaching the model, and every interaction is logged within the organization’s environment.
This is how companies like Innovaccer operate, maintaining full auditability and preventing data from leaving their controlled infrastructure.
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.
The fastest way to build, govern and scale your AI

















.webp)












.png)