MCP Authentication Explained: How It Works and Why It Matters
.webp)
Built for Speed: ~10ms Latency, Even Under Load
Blazingly fast way to build, track and deploy your models!
- Handles 350+ RPS on just 1 vCPU — no tuning needed
- Production-ready with full enterprise support
MCP authentication and authorization have not always been as secure as they are today. When MCP first started rolling out, authentication usually occurred via API keys, which were often included in a configuration file or as environment variables, thereby allowing static, shared, unscoped access. If this key was leaked, it would grant a malicious user full access, with no way to track or control what was done.
The MCP specification evolved quickly to address this:
- March 2025: OAuth 2.1 was defined as the standard for authenticating an application or user against an API.
- June 2025: MCP servers were redefined as OAuth resource servers, and the ability to issue tokens moved to external identity providers.
- November 2025: PKCE became mandatory for all client-side applications, and CIMD was defined as a way to uniquely identify each client instance.
In less than a year, the MCP authentication method transitioned from static secrets to a model consistent with modern enterprise identity systems.
This guide outlines what MCP authentication is, how it works, the possible approaches to implementing it, where implementations go wrong, and how to properly implement it at scale.
.webp)
.webp)
What Is MCP Authentication?
MCP authentication is the process by which an MCP server verifies the identity of a requester before executing any tool.
Without MCP authentication in place, any MCP client that could reach an MCP server could invoke its tools, regardless of the identity, role, or intent of that client. If the tools invoked establish a connection with critical external systems such as CRMs, databases, or cloud services, that would create an unrestricted pathway to production sensitive data.
This is not a theoretical risk. A CVSS 9.6 vulnerability in the mcp-remote package allowed malicious MCP servers to leverage the OAuth flow within the package to execute arbitrary OS commands remotely, impacting hundreds of thousands of downloads.
MCP authentication is performed via the transport layer before tool execution occurs. The manner of execution depends on how the MCP server is deployed:
- STDIO transport (local servers): Runs as a local process; MCP authentication may use environment variables or system credentials outside of MCP.
- Streamable HTTP (remote servers): Runs over the network with no shared trust between MCP client and server. MCP authentication occurs using OAuth 2.1 with access tokens attached to each request.
In practice:
- Local development: environment-based credentials may be sufficient.
- Remote production systems: OAuth 2.1 is required for proper authentication.
.webp)
The Three Types of MCP Authentication
Authentication Methods used in different MCP Deployments depending on Environment and Risk Tolerance
API Keys and Static Tokens
It is a simple method of passing a pre-agreed key with every request.
Authorization: Bearer sk-xxxx
When it works:
- In local development, and by an internal tool operating within a well-defined network boundary.
Limitations:
- Static tokens have no expiry
- Static tokens have no user identity
- No granular permissions
- Static tokens can be leaked via logs or version control, which is quite risky.
- When static tokens are exposed, full access control to the associated system will remain active until manually disabled
OAuth 2.1 with PKCE (Standard for Remote MCP Servers)
Beginning with the March 2025 MCP specification update, the standard for securing remote MCP servers via MCP authentication is OAuth 2.1 with PKCE. Instead of static credentials, this approach uses a secure, token-based authorization flow that enables Streamable HTTP.
How it works:
- Metadata discovery: The MCP client attempts to discover the required authorization server metadata from the server without an access token and receives a 401 response. The protected resource metadata document tells the client which authorization server to connect to and which required scopes are available.
- Client registration: The MCP client registers with the authorization server. The default method since November 2025 is via the CIMD protocol. The client publishes its client id metadata on a public URL it controls, and the authorization server performs runtime validation of the client information.
- Authorization code: The client opens the user's browser, requests the user to log in and give consent, and receives an authorization code from the authorization server to act on their behalf.
- Access token issuance: The client exchanges the authorization code using the authorization code flow for an access token scoped to the requested resource, and includes this token with every MCP request.
Why PKCE matters:
- PKCE protects against interception attacks by ensuring that the user completing the MCP authentication is the same person who initiated it.
- PKCE is required for all MCP clients from November 2025 onward per the current MCP spec.
Environment-Based Credentials (STDIO Servers)
Local MCP servers inherit credentials from their own runtime environment.
.webp)
Pros:
- Easy to set up with no external authorization flow.
Cons:
- Credentials are accessible to any process that can access the MCP system, creating risk across data sources.
- Difficult to manage across multiple people or teams without centralized authorization logic.
- No centralized governance or access control.
In Production environments, you should retrieve your credentials dynamically using a secure vault instead of storing them in plain text.
.webp)
How MCP OAuth 2.1 Authentication Works Step by Step
When a MCP client connects to a protected MCP server, the following MCP flow occurs:
- Step 1 — Client connects, server rejects: The MCP client attempts a request with no token. The server responds with a 401 Unauthorized error and a pointer to its protected resource metadata URL as part of authorization server discovery.
- Step 2 — Client retrieves metadata: The metadata endpoint specifies which authorization server to use, what OAuth scopes are available, and where to locate the token endpoint.
- Step 3 — Client registers and begins the OAuth flow: The client identifies itself using CIMD and its client id metadata document, creates a PKCE code verifier and code challenge, then redirects the user's browser to the authorization server's login page.
- Step 4 — User authenticates and receives the authorization code: The user logs in and consents. The authorization server returns an authorization code for the client to exchange using the original code verifier for a short-lived, scoped access token.
- Step 5 — Client calls the MCP server with bearer token: Every MCP request includes the access token in the Authorization Bearer header. The MCP server validates the issuer, audience, expiry, and OAuth scopes. If the access token carries insufficient required scopes, the server responds with a 403 and requests additional user authorization, a capability introduced in November 2025.
.webp)
Where MCP Authentication Still Goes Wrong?
Many deployments create serious MCP security risks through improper MCP authentication and authorization implementation, even when using OAuth.
- Static tokens in config files: API keys committed to Git repositories, shared in mcp.json or .env files, and forgotten. A single compromised OAuth client id provides unlimited access and never expires, creating a persistent source of unauthorized access.
- Over-permissioned OAuth scopes: Users request a large number of OAuth scopes during configuration but do not restrict them when running the application. An AI agent configured as read-only should be stored with a read-scoped access token rather than a read/write/delete token.
- No token rotation in self-managed deployments: Long-lived OAuth tokens issued to self-managed deployments with no rotation process. If a token becomes compromised, it remains functional as a valid bearer token until someone manually disables it.
- No audit trail for tool calls: When a token is issued and external tools are accessed, no record exists indicating who made the original MCP request, making root cause investigation impossible for security team members.
Most of these issues are resolved when organizations migrate from static keys to OAuth 2.1, which enables short-lived access tokens, scoped OAuth scopes, and centralized audit logging through the authorization server.
.webp)
.webp)
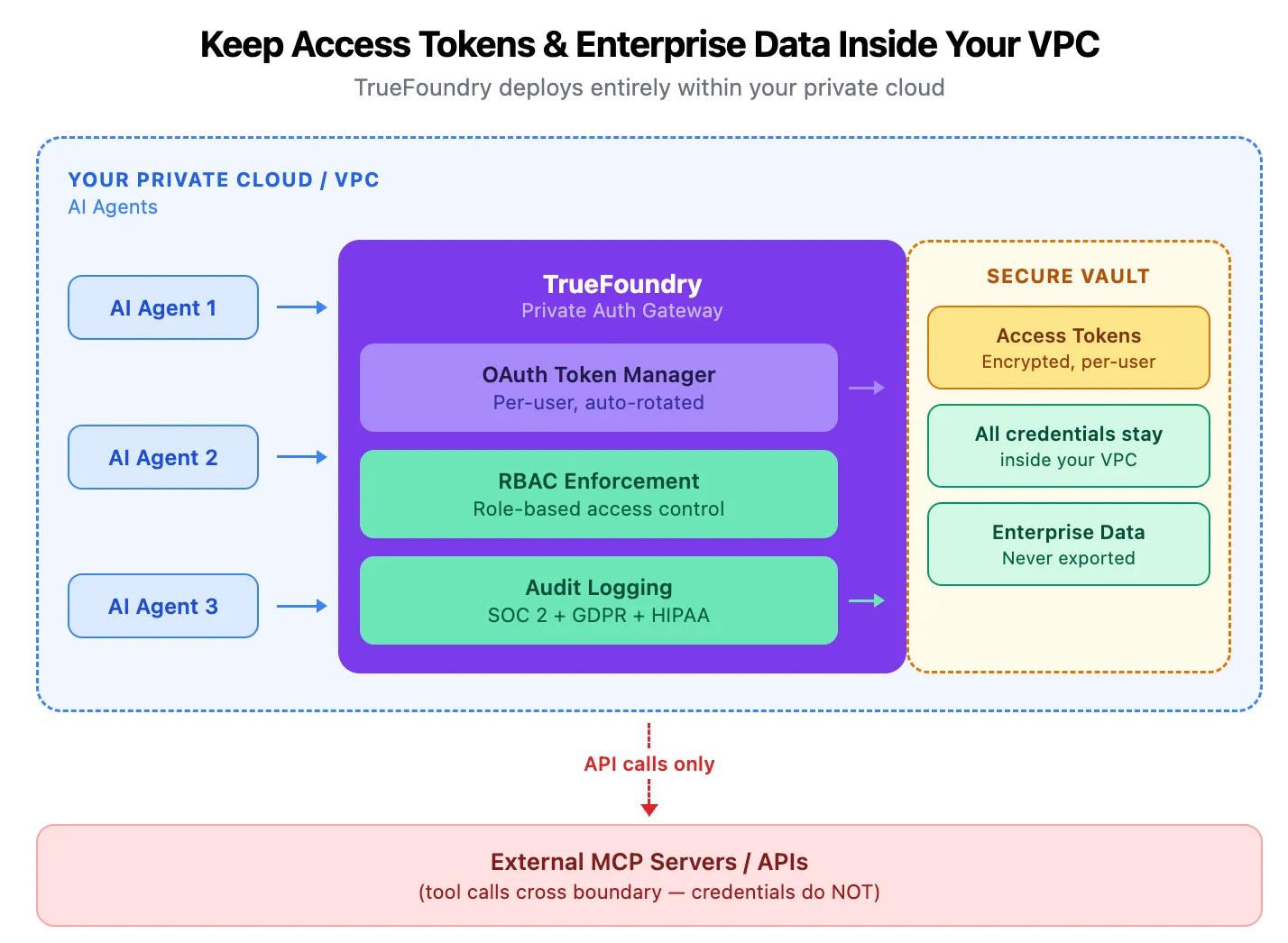
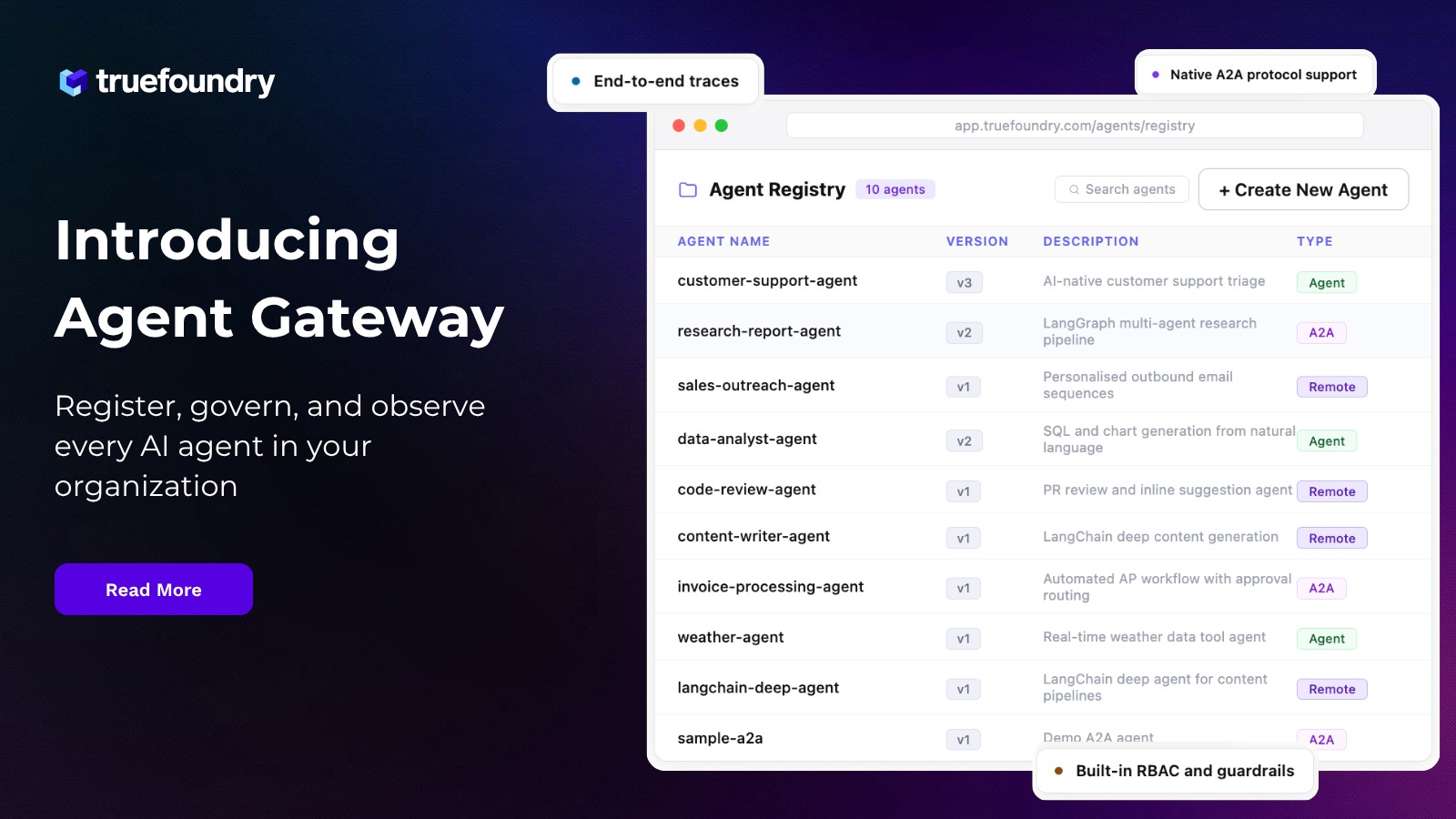
Enterprise MCP Authentication Requirements vs. How TrueFoundry Solves Them
TrueFoundry removes the complexity of managing multiple forms of MCP authentication and authorization across individual teams and applies uniform controls across all MCP servers through a single MCP gateway layer.
Book a demo to understand how MCP handles authentication at the infrastructure level
Frequently Asked Questions
What is MCP authentication?
MCP authentication is the process of verifying the identity of an entity attempting to connect to an MCP server, using OAuth tokens, API keys, or environment variables depending on deployment context. It enables only verified AI agents and MCP clients to access tools and external services, forming the first layer of MCP authentication and authorization in any production system.
Does MCP require OAuth?
Not in every case. A local STDIO transport server may not implement a formal OAuth flow. However, any remote MCP server handling production-sensitive data or external tools should use OAuth 2.1 with PKCE as the standard authorization mechanism under the current MCP specification for proper MCP authentication and authorization enforcement.
Does MCP have authentication?
MCP supports MCP authentication and authorization, and the method depends on the server environment. Remote servers use OAuth 2.1 PKCE as the standard authorization flow. Local STDIO transport servers authenticate using credentials from environment variables or the host process. The MCP spec formally mandated OAuth 2.1 as the standard for remote deployments from March 2025 onward.
What are the types of MCP authentication?
Three common methods exist for MCP authentication and authorization: static API keys for internal or development use cases, OAuth 2.1 with PKCE for all remote MCP server deployments as required by the MCP specification, and environment-based credentials via environment variables for local STDIO transport servers where a formal OAuth client registration flow is not required.
How does MCP authentication work?
When a MCP client connects to a protected MCP server, the server returns a 401 with a pointer to its protected resource metadata document. The client performs authorization server discovery, registers using CIMD, completes the authorization code flow with PKCE, and receives a scoped access token. This token is included with every incoming request for token validation before any tool call is permitted.
How does TrueFoundry handle MCP authentication?
Through the MCP gateway, TrueFoundry centralizes MCP authentication and authorization by integrating with enterprise identity providers and handling automated access token issuance, rotation, and token validation. OAuth scopes and RBAC policies are enforced at the gateway layer across all MCP servers, with structured audit logs retained inside the customer VPC for compliance across AI agents and external services.
TrueFoundry AI Gateway delivers ~3–4 ms latency, handles 350+ RPS on 1 vCPU, scales horizontally with ease, and is production-ready, while LiteLLM suffers from high latency, struggles beyond moderate RPS, lacks built-in scaling, and is best for light or prototype workloads.
The fastest way to build, govern and scale your AI
















.webp)















.png)














