Enterprise organizations often have MCP servers distributed across multiple cloud providers and on-premises data centers. These MCP servers may be accessible only from within their respective network environments due to security policies, compliance requirements, or network isolation. The TrueFoundry Federated MCP Gateway architecture enables seamless cross-cloud access to MCP servers while maintaining network isolation and security boundaries.Documentation Index
Fetch the complete documentation index at: https://www.truefoundry.com/llms.txt
Use this file to discover all available pages before exploring further.
The Challenge: Multi-Cloud MCP Server Access
Consider an organization with the following infrastructure:- AWS: Internal analytics MCP server, customer data tools
- Azure: Microsoft 365 integration MCP server, Azure DevOps tools
- GCP: BigQuery MCP server, Google Workspace tools
- On-premises: Legacy systems MCP server, sensitive data tools
- Applications in AWS need to access MCP servers in Azure, GCP, and on-premises
- Applications in Azure need to access MCP servers in AWS, GCP, and on-premises
- Network isolation must be maintained—direct cross-cloud connections are not allowed
- A single control plane should manage all MCP server registrations and access policies
- Users should have a unified experience regardless of where MCP servers are deployed
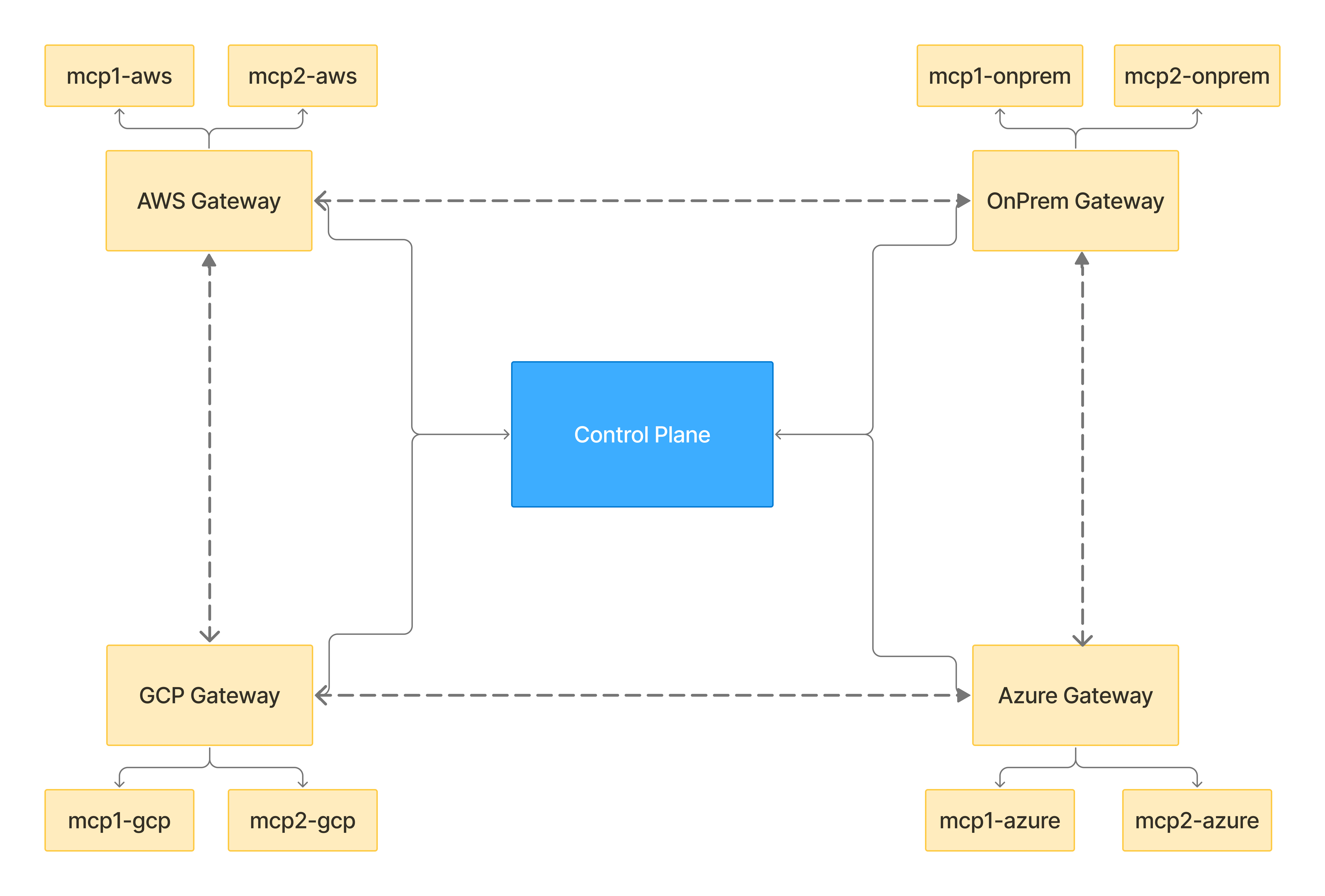
Federated Gateway Architecture
The TrueFoundry Federated MCP Gateway solves this challenge by deploying gateway planes in each cloud environment, with all gateway planes connected to a central control plane.Key Components
| Component | Description |
|---|---|
| Central Control Plane | Single control plane deployed in a central region. Manages all MCP server registrations, access policies, and configuration. Syncs configuration to all gateway planes. |
| Gateway Planes | One gateway plane deployed in each cloud/environment (AWS, Azure, GCP, on-premises). Each gateway plane can only access MCP servers within its own environment. |
| Inter-Gateway Communication | All gateway planes can communicate with each other and with the control plane. This enables request proxying across environments. |
| MCP Servers | MCP servers deployed within each cloud environment. Only accessible from the gateway plane in the same environment. |
Network Topology
How Federated Routing Works
When an MCP server is registered in the TrueFoundry control plane, you specify a proxy URL that indicates which gateway plane can directly access that MCP server. The control plane syncs this information to all gateway planes, enabling intelligent request routing.Proxy URL Configuration
When registering an MCP server, you configure:| Field | Description | Example |
|---|---|---|
| MCP Server URL | The internal URL of the MCP server | http://analytics-mcp.internal:8080 |
| Proxy URL | The gateway plane URL that can access this MCP server | https://aws-gw.example.com |
mcp-analytics(deployed in AWS) → Proxy URL:https://aws-gw.example.commcp-m365(deployed in Azure) → Proxy URL:https://azure-gw.example.commcp-bigquery(deployed in GCP) → Proxy URL:https://gcp-gw.example.com
Request Flow: Cross-Cloud Access
Let’s trace a request from an application in AWS accessing an MCP server deployed in Azure. Scenario: An AI agent running in AWS needs to call a tool onmcp-m365 (deployed in Azure).
Application sends request to local gateway
aws-gw.example.com). The request includes the MCP server identifier (mcp-m365) and authentication credentials.AWS Gateway looks up MCP server configuration
mcp-m365 from its synced configuration. It sees that the proxy URL is azure-gw.example.com, which is different from itself.AWS Gateway proxies request to Azure Gateway
azure-gw.example.com). The request includes all necessary authentication and context.Azure Gateway receives and evaluates request
mcp-m365. It sees the proxy URL is azure-gw.example.com, which matches its own URL.Azure Gateway forwards to MCP server
mcp-m365) running in Azure.Proxy URL Matching Logic
Each gateway plane uses the following logic when handling a request:Configuration Guide
Step 1: Deploy Gateway Planes in Each Environment
Deploy a TrueFoundry Gateway Plane in each cloud environment where you have MCP servers.- AWS
- Azure
- GCP
- On-premises
- All MCP servers within AWS VPC
- The central control plane
- Other gateway planes (Azure, GCP, on-premises)
Step 2: Configure Inter-Gateway Connectivity
All gateway planes must be able to communicate with each other. Configure your network to allow:| Source | Destination | Port | Protocol |
|---|---|---|---|
| AWS Gateway | Azure Gateway | 443 | HTTPS |
| AWS Gateway | GCP Gateway | 443 | HTTPS |
| AWS Gateway | On-prem Gateway | 443 | HTTPS |
| Azure Gateway | AWS Gateway | 443 | HTTPS |
| Azure Gateway | GCP Gateway | 443 | HTTPS |
| Azure Gateway | On-prem Gateway | 443 | HTTPS |
| GCP Gateway | AWS Gateway | 443 | HTTPS |
| GCP Gateway | Azure Gateway | 443 | HTTPS |
| GCP Gateway | On-prem Gateway | 443 | HTTPS |
| On-prem Gateway | AWS Gateway | 443 | HTTPS |
| On-prem Gateway | Azure Gateway | 443 | HTTPS |
| On-prem Gateway | GCP Gateway | 443 | HTTPS |
Step 3: Register MCP Servers with Proxy URLs
When registering MCP servers in the TrueFoundry control plane, specify the proxy URL for each server.Add a new MCP server
| Field | Value |
|---|---|
| Name | mcp-m365 |
| Server URL | http://m365-mcp.azure-internal:8080 |
| Proxy URL | https://azure-gw.example.com |
| Authentication | Configure as needed |
| MCP Server | Internal URL | Proxy URL |
|---|---|---|
mcp-analytics | http://analytics.aws-internal:8080 | https://aws-gw.example.com |
mcp-m365 | http://m365.azure-internal:8080 | https://azure-gw.example.com |
mcp-devops | http://devops.azure-internal:8080 | https://azure-gw.example.com |
mcp-bigquery | http://bigquery.gcp-internal:8080 | https://gcp-gw.example.com |
mcp-legacy | http://legacy.onprem-internal:8080 | https://onprem-gw.example.com |
Step 4: Configure Applications to Use Local Gateway
Applications should always connect to their local gateway plane. The gateway handles all cross-cloud routing automatically.Authentication in Federated Setup
All standard authentication methods work in the federated setup. The authentication token is passed through the entire proxy chain.Token Flow in Proxied Requests
TrueFoundry API Key / PAT
TrueFoundry API Key / PAT
Identity Provider Token
Identity Provider Token
OAuth2 Outbound Authentication
OAuth2 Outbound Authentication
Observability and Monitoring
The federated setup provides full observability across all gateway planes.Request Tracing
Each request includes trace context that flows through the entire proxy chain. You can view:- End-to-end latency (including inter-gateway hops)
- Which gateway planes handled the request
- Time spent at each hop
- MCP server response time
Metrics
All gateway planes report metrics to the central control plane:| Metric | Description |
|---|---|
mcp_requests_total | Total MCP requests by server, user, and gateway |
mcp_proxy_requests_total | Requests proxied to other gateways |
mcp_proxy_latency_ms | Latency added by inter-gateway proxying |
mcp_gateway_to_gateway_errors | Errors in gateway-to-gateway communication |
Audit Logging
All requests are logged with complete audit trail:Best Practices
Gateway Placement
Gateway Placement
- Deploy gateway planes as close as possible to the MCP servers they serve
- Use dedicated gateway instances for high-traffic MCP servers
- Consider deploying multiple gateway replicas for high availability
Network Configuration
Network Configuration
- Use private connectivity (VPC peering, ExpressRoute, Cloud Interconnect) between clouds when possible
- Ensure low-latency connections between gateway planes
- Configure appropriate timeouts for inter-gateway communication
Security
Security
- Use mutual TLS for all gateway-to-gateway communication
- Implement network segmentation—MCP servers should only be accessible from their local gateway
- Regularly rotate certificates and credentials
Monitoring
Monitoring
- Set up alerts for inter-gateway communication failures
- Monitor proxy latency and set thresholds for acceptable performance
- Track cross-cloud traffic for cost optimization
FAQ
What happens if a gateway plane is unavailable?
What happens if a gateway plane is unavailable?
Does proxying add significant latency?
Does proxying add significant latency?
Can I have multiple gateways in the same cloud?
Can I have multiple gateways in the same cloud?
How does configuration sync work across gateways?
How does configuration sync work across gateways?
Can applications access multiple MCP servers in different clouds in a single session?
Can applications access multiple MCP servers in different clouds in a single session?
How are errors handled in the proxy chain?
How are errors handled in the proxy chain?